

Several stable pools on Curve Finance using Vyper were exploited on July 30. Vyper versions 0.2.15, 0.2.16 and 0.3.0 are vulnerable to malfunctioning reentrancy locks.
Update (July 30, at 7:55 pm UTC): This article has been updated to provide more details about the exploit
Several stable pools on Curve Finance using Vyper were exploited on July 30, with losses reaching over $47 million. According to Vyper, its 0.2.15, 0.2.16 and 0.3.0 versions are vulnerable to malfunctioning reentrancy locks.
“The investigation is ongoing but any project relying on these versions should immediately reach out to us,” Vyper wrote on X. Based on an analysis of affected contracts by security firm Ancilia, 136 contracts used Vyper 0.2.15 with reentrant protection, 98 contracts used Vyper 0.2.16 and 226 contracts used Vyper 0.3.0.
A number of stablepools (alETH/msETH/pETH) using Vyper 0.2.15 have been exploited as a result of a malfunctioning reentrancy lock. We are assessing the situation and will update the community as things develop.
Other pools are safe. https://t.co/eWy2d3cDDj
— Curve Finance (@CurveFinance) July 30, 2023
According to initial investigation, some versions of the Vyper compiler do not correctly implement the reentrancy guard, which prevents multiple functions from being executed at the same time by locking a contract. Reentrancy attacks can potentially drain all funds from a contract.
Vyper is a contract-oriented, pythonic programming language that targets the Ethereum Virtual Machine (EVM). Vyper’s similarities to Python make the language one of the starting points for Python developers jumping into Web3.
A number of decentralized finance projects were affected by the attack. Decentralized exchange Ellipsis reported that a small number of stable pools with BNB were exploited using an old Vyper compiler. Alchemix’s alETH-ETH also witnessed $13.6 million outflow, along with $11.4 million exploited on JPEGd’s pETH-ETH pool, and $1.6 million in Metronome’s sETH-ETH pool. Curve Finance CEO Michael Egorov later confirmed 32 million CRV tokens worth over $22 million had been drained from the swap pool in a Telegram channel.
Certain type of Curve factory pool is encountering read-only reentrancy attack and causing a total loss of $11m(@JPEGd_69) + $13m(@AlchemixFi) + …
Initial investigation founds that vyper compiler (0.2.15) doesn’t implement the reentrancy guard correctly.
add_liquidity and… pic.twitter.com/avaHdtSFsm
— Tony KΞ (@tonyke_bot) July 30, 2023
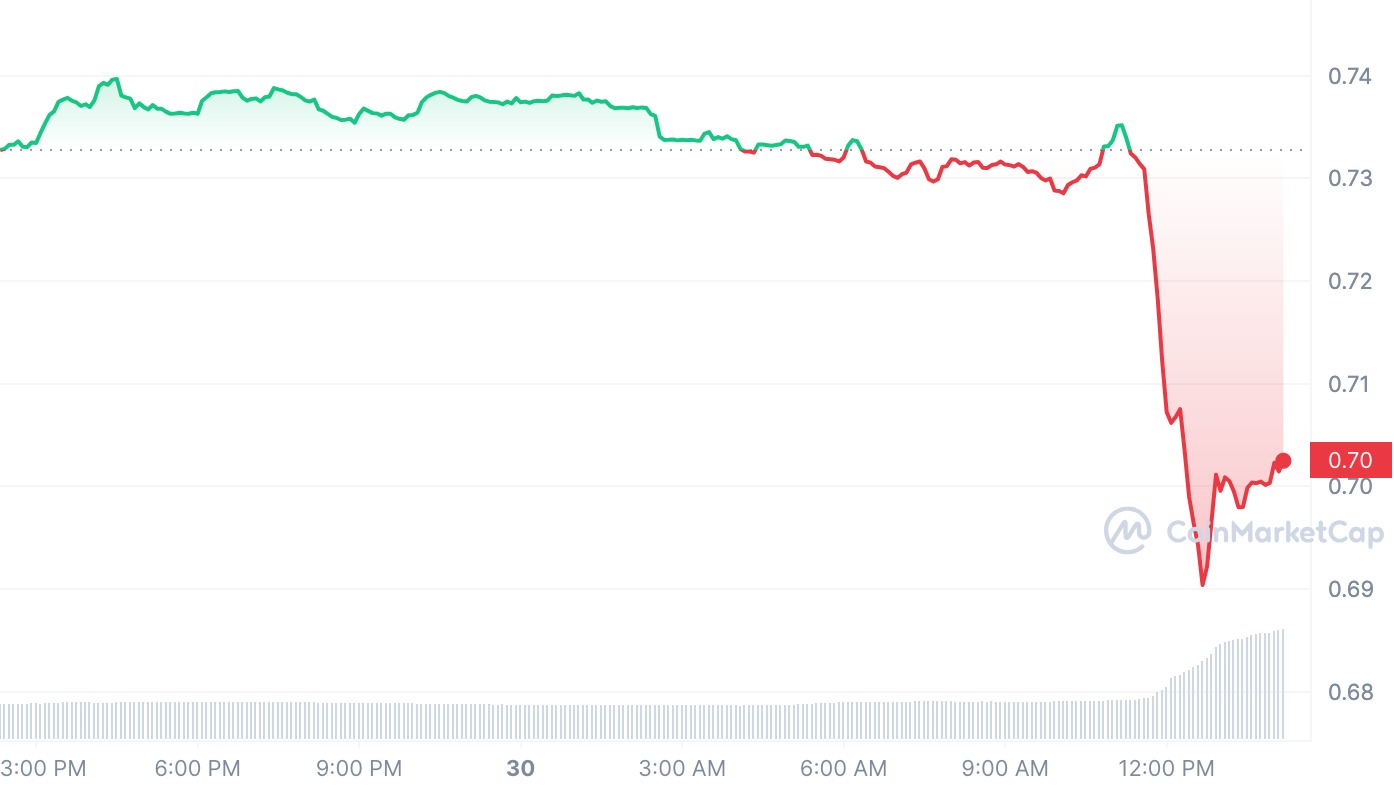
The exploit sparked panic across the DeFi ecosystem, prompting a wave of transactions across pools and a rescue operation from white hats. Data from CoinMarketCap shows Curve Finance’s utility token Curve DAO (CRV) declining over 5% in reaction to the news. CRV’s liquidity has declined significantly in recent months, making it vulnerable to violent price swings, Cointelegraph reported. According to Curve Finance, crvUSD contracts and any pools with it were not affected by the attack.
Curve Finance is a DeFi protocol that enables the decentralized exchange of stablecoins within Ethereum. The protocol has been targeted by a series of incidents within its ecosystem. Just a few days ago, its omnipool platform Conic Finance was exploited for $3.26 million in Ether (ETH), with nearly the entire amount stolen sent to a new Ethereum address in just one transaction.
DeFi protocols have been targeted by multiple attacks over the past months. According to a report by Web3 portfolio app De.Fi, more than $204 million was swindled through DeFi hacks and scams in the second quarter of 2023 alone.
Magazine: Should crypto projects ever negotiate with hackers? Probably




