Cryptography experts are somewhat skeptical of the technique’s scalability but aren’t ruling out the possibility of success either.
According to a recent paper, Chinese researchers claimed to have discovered a novel method to break the Rivest-Shamir-Adleman 2048 bit (RSA-2048) signing algorithm present in blockchains and other security protocols. RSA is a cryptographic technique that utilizes a public key to encrypt information and a private key to decrypt it.
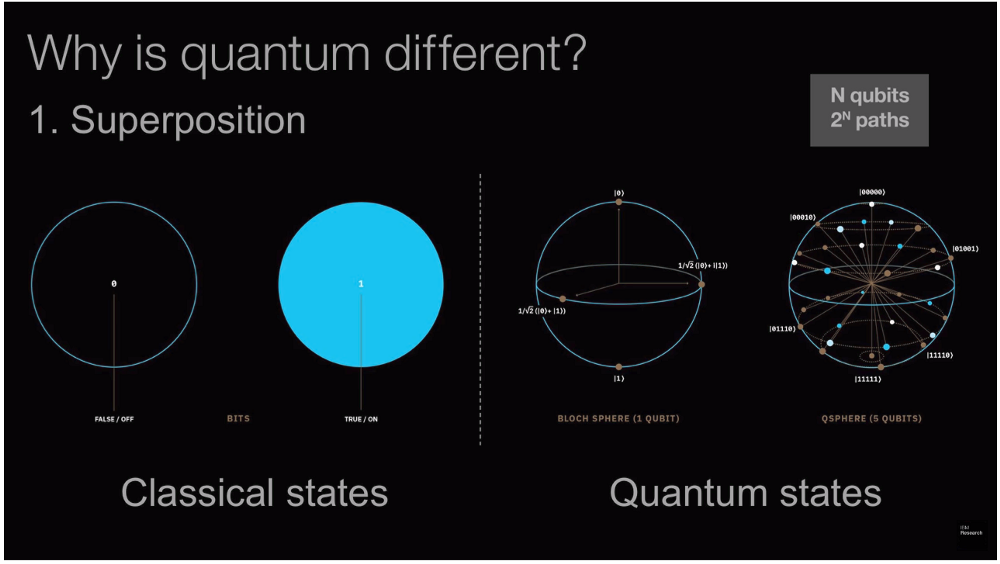
Breaching the RSA-2048 algorithm requires, similar to other algorithms in the RSA numbers family, finding the prime factors of a number with 617 decimal digits and 2048 binary digits. Experts estimate that it would take ordinary computers 300 trillion years to break an RSA-2048 encryption key. However, Chinese researchers said in their paper that the encryption could be inversed with a quantum computer with 372 qubits, or a basic unit of information acting as a proxy for computation power.
In comparison, the latest IBM Osprey quantum computer has a processing capacity of 433 qubits. Previously, experts calculated that factoring RSA-2048 with quantum computers employing a quantum factoring method known as Shor’s algorithm would require 13,436 qubits.
Unlike classical computers that operate on a binary basis of 0 or 1, quantum computers utilize quantum bits that can take on infinite states at temperatures of -273°C (-459.4°F), achieved by using liquid gas coolants. Thus, the quantum computer is able to map out all possible solutions to a cryptographic problem and attempt them all at once, increasing efficiency on an astronomic scale.
According to American cryptographer Bruce Schneier, Chinese researchers appear to have combined “classical lattice reduction factoring techniques with a quantum approximate optimization algorithm” that successfully factored 48-bit numbers using a 10-qubit quantum computer. “And while there are always potential problems when scaling something like this up by a factor of 50, there are no obvious barriers,” Schneier commented.
Security expert Roger Grimes added:
“Apparently what happened is another guy who had previously announced he was able to break traditional asymmetric encryption using classical computers … but reviewers found a flaw in his algorithm and that guy had to retract his paper. But this Chinese team realized that the step that killed the whole thing could be solved by small quantum computers. So they tested and it worked.”
Schneier also warned that the algorithm relies on a recent factoring paper authored by Peter Schnorr, where its algorithm works well with small bits, but falls apart at larger sizes, with no tangible explanation. “So if it’s true that the Chinese paper depends on this Schnorr technique that doesn’t scale, the techniques in this Chinese paper won’t scale, either,” Schneier wrote.
“In general, the smart bet is on the new techniques not working. But someday, that bet will be wrong.”
Quantum computers are also limited by operational factors such as heat loss and the requirement of a complex -273°C (-459.4°F) cooling infrastructure. Thus, the number of nominal qubits required to inverse cryptographic algorithms is likely far higher than theoretical estimates.
Although researchers have not yet done so, the methodology could be theoretically replicable to other RSA-2048 protocols used in informational technology, such as HTTPS, email, web browsing, two-factor authentication, etc. Ethereum co-founder Vitalik Buterin previously stated his long-term goals include making the blockchain quantum resistant. Theoretically, this involves forking the network to utilize a higher-order encryption algorithm that would require greater qubits to break.
Cointelegraph editor Jeffrey Albus contributed to this story.




